
Unified Agent & MCP Server Registry – Enterprise-Ready Gateway for AI Development Tools
🚀 Get Running Now | Production Deployment | Quick Start | Documentation | Enterprise Features | Community
Demo Videos: ⭐ MCP Registry CLI Demo | Full End-to-End Functionality | OAuth 3-Legged Authentication | Dynamic Tool Discovery
What is MCP Gateway & Registry?
The MCP Gateway & Registry is a unified, enterprise-ready platform that centralizes access to both MCP Servers and AI Agents using the Model Context Protocol (MCP). It serves three core functions:
- Unified MCP Server Gateway – Centralized access point for multiple MCP servers
- MCP Servers Registry – Register, discover, and manage access to MCP servers with unified governance
- Agent Registry & A2A Communication Hub – Agent registration, discovery, governance, and direct agent-to-agent communication through the A2A (Agent-to-Agent) Protocol
The platform integrates with external registries such as Anthropic's MCP Registry (and more to come), providing a single control plane for both tool access, agent orchestration, and agent-to-agent communication patterns.
Why unified? Instead of managing hundreds of individual MCP server configurations, agent connections, and separate governance systems across your development teams, this platform provides secure, governed access to curated MCP servers and registered agents through a single, unified control plane.
Transform this chaos:
❌ AI agents require separate connections to each MCP server
❌ Each developer configures VS Code, Cursor, Claude Code individually
❌ Developers must install and manage MCP servers locally
❌ No standard authentication flow for enterprise tools
❌ Scattered API keys and credentials across tools
❌ No visibility into what tools teams are using
❌ Security risks from unmanaged tool sprawl
❌ No dynamic tool discovery for autonomous agents
❌ No curated tool catalog for multi-tenant environments
❌ A2A provides agent cards but no way for agents to discover other agents
❌ Maintaining separate MCP server and agent registries is a non-starter for governance
❌ Impossible to maintain unified policies across server and agent access
Into this organized approach:
✅ AI agents connect to one gateway, access multiple MCP servers
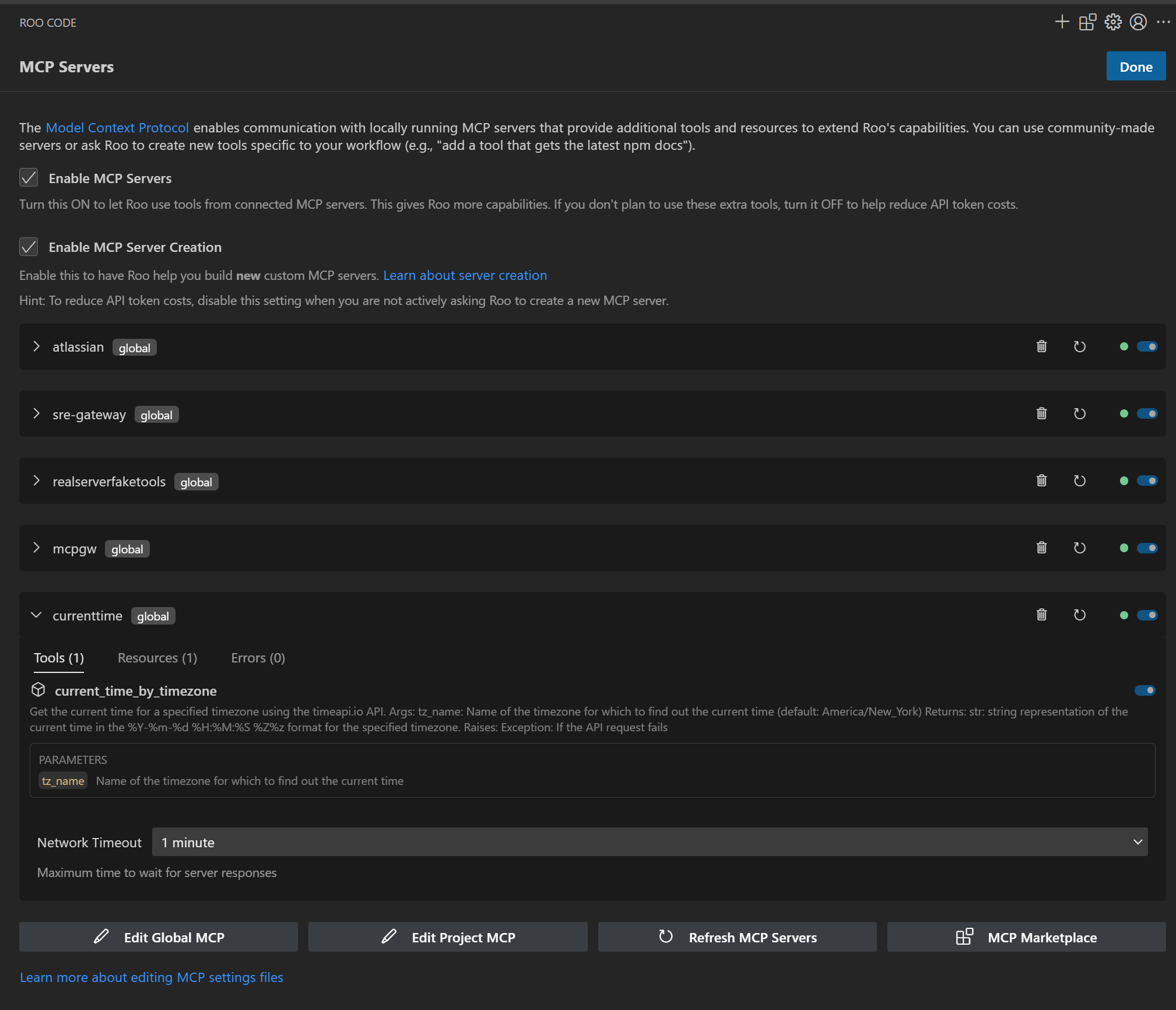
✅ Single configuration point for VS Code, Cursor, Claude Code
✅ Central IT manages cloud-hosted MCP infrastructure via streamable HTTP
✅ Developers use standard OAuth 2LO/3LO flows for enterprise MCP servers
✅ Centralized credential management with secure vault integration
✅ Complete visibility and audit trail for all tool usage
✅ Enterprise-grade security with governed tool access
✅ Dynamic tool discovery and invocation for autonomous workflows
✅ Registry provides discoverable, curated MCP servers for multi-tenant use
✅ Agents can discover and communicate with other agents through unified Agent Registry
✅ Single control plane for both MCP servers and agent governance
✅ Unified policies and audit trails for both server and agent access
┌─────────────────────────────────────┐ ┌──────────────────────────────────────────────────────┐
│ BEFORE: Chaos │ │ AFTER: MCP Gateway & Registry │
├─────────────────────────────────────┤ ├──────────────────────────────────────────────────────┤
│ │ │ │
│ Developer 1 ──┬──► MCP Server A │ │ Developer 1 ──┐ ┌─ MCP Server A │
│ ├──► MCP Server B │ │ │ ├─ MCP Server B │
│ └──► MCP Server C │ │ Developer 2 ──┼──► MCP Gateway │ │
│ │ │ │ & Registry ───┼─ MCP Server C │
│ Developer 2 ──┬──► MCP Server A │ ──► │ AI Agent 1 ───┘ │ │ │
│ ├──► MCP Server D │ │ │ ├─ AI Agent 1 │
│ └──► MCP Server E │ │ AI Agent 2 ──────────────┤ ├─ AI Agent 2 │
│ │ │ │ │ │
│ AI Agent 1 ───┬──► MCP Server B │ │ AI Agent 3 ──────────────┘ └─ AI Agent 3 │
│ ├──► MCP Server C │ │ │
│ └──► MCP Server F │ │ Single Connection Point │
│ │ │ │
│ ❌ Multiple connections per user │ │ ✅ One gateway for all │
│ ❌ No centralized control │ │ ✅ Unified server & agent access │
│ ❌ Credential sprawl │ │ ✅ Unified governance & audit trails │
└─────────────────────────────────────┘ └──────────────────────────────────────────────────────┘
Note on Agent-to-Agent Communication: AI Agents discover other AI Agents through the unified Agent Registry and communicate with them directly (peer-to-peer) without routing through the MCP Gateway. The Registry handles discovery, authentication, and access control, while agents maintain direct connections for efficient, low-latency communication.
Unified Agent & Server Registry
This platform serves as a comprehensive, unified registry supporting:
- ✅ MCP Server Registration & Discovery – Register, discover, and manage access to MCP servers
- ✅ AI Agent Registration & Discovery – Register agents and enable them to discover other agents
- ✅ Agent-to-Agent (A2A) Communication – Direct agent-to-agent communication patterns using the A2A protocol
- ✅ Multi-Protocol Support – Support for various agent communication protocols and patterns
- ✅ Unified Governance – Single policy and access control system for both agents and servers
- ✅ Cross-Protocol Agent Discovery – Agents can discover each other regardless of implementation
- ✅ Integrated External Registries – Connect with Anthropic's MCP Registry and other external sources
- ✅ Agent Cards & Metadata – Rich metadata for agent capabilities, skills, and authentication schemes
Key distinction: Unlike separate point solutions, this unified registry eliminates the need to maintain separate MCP server and agent systems, providing a single control plane for agent orchestration, MCP server access, and agent-to-agent communication.
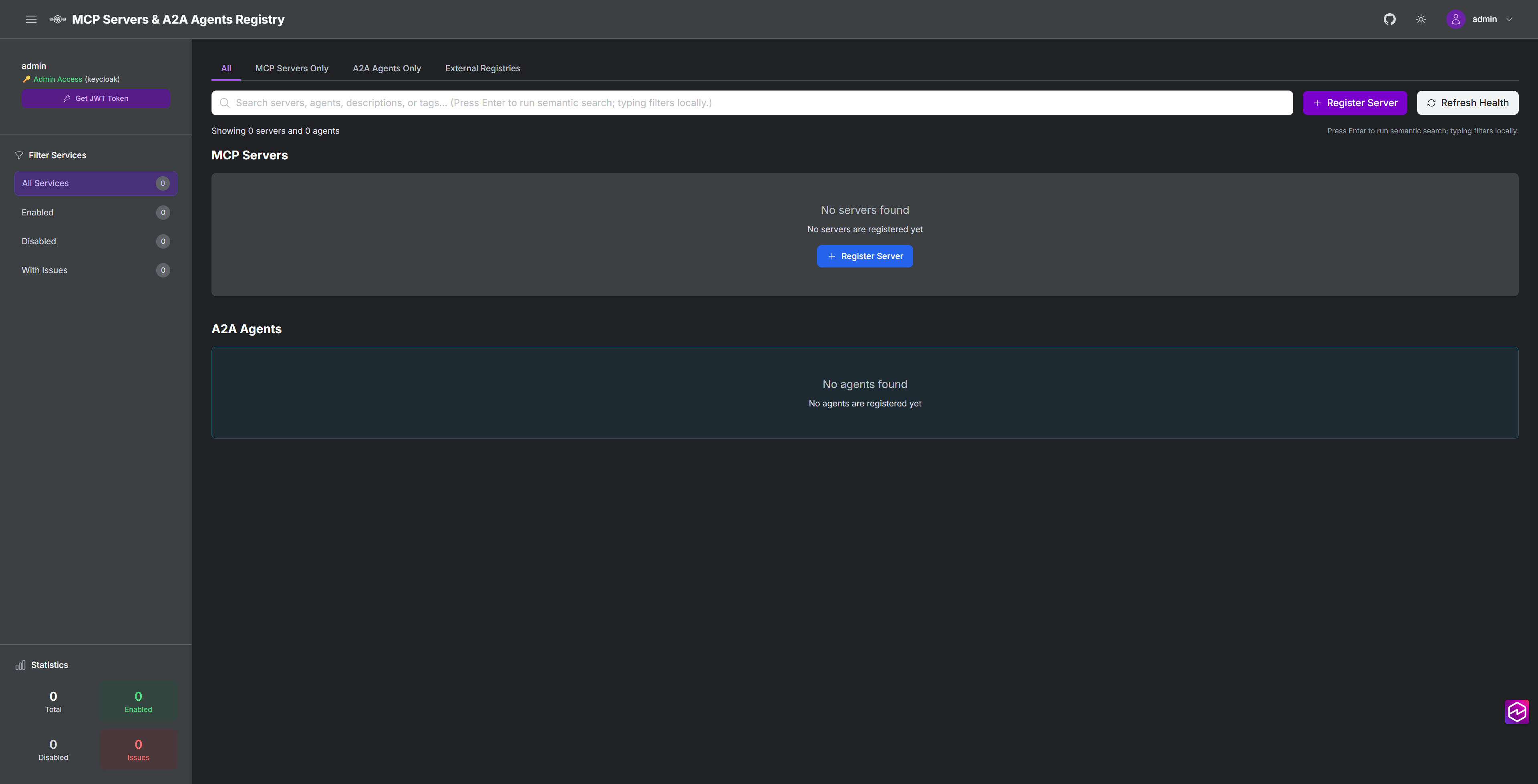
MCP Servers & Agents Registry
Watch how MCP Servers, A2A Agents, and External Registries work together for dynamic tool discovery:
https://github.com/user-attachments/assets/f539f784-17f5-4658-99b3-d664bd5cecaa
MCP Tools in Action
MCP Registry CLI
Interactive terminal interface for chatting with AI models and discovering MCP tools in natural language. Talk to the registry using a Claude Code-like conversational interface with real-time token status, cost tracking, and AI model selection.

Quick Start: registry --url https://mcpgateway.ddns.net | Full Guide
What's New
- 🛡️ Security Scan Results in UI - Security scan results are now displayed directly on Server and Agent cards with color-coded shield icons (gray/green/red). Click the shield icon to view detailed scan results and trigger rescans from the UI. Security Scanner Documentation
- 🧪 Comprehensive Test Suite & Updated LLM Documentation - Full pytest test suite with 701+ passing tests (unit, integration, E2E) running automatically on all PRs via GitHub Actions. 35% minimum coverage (targeting 80%), ~30 second execution with 8 parallel workers. Updated llms.txt provides comprehensive documentation for LLM coding assistants covering storage backend migration (file → DocumentDB/MongoDB), repository patterns, AWS ECS deployment, Microsoft Entra ID integration, dual security scanning, federation architecture, rating system, testing standards, and critical code organization antipatterns. Testing Guide | docs/llms.txt
- 📊 DocumentDB & MongoDB CE Storage Backend - Production-grade distributed storage with MongoDB-compatible backends. DocumentDB provides native HNSW vector search for sub-100ms semantic queries in production deployments, while MongoDB Community Edition 8.2 enables full-featured local development with replica sets. Both backends use the same repository abstraction layer with automatic collection management, optimized indexes, and application-level vector search for MongoDB CE. Switch between MongoDB CE (local testing) and DocumentDB (production) with a single environment variable. Note: File-based storage is deprecated and will be removed in a future release. MongoDB CE is recommended for local development. Configuration Guide | Storage Architecture
- 🔒 A2A Agent Security Scanning - Integrated security scanning for A2A agents using Cisco AI Defense A2A Scanner. Automatic security scans during agent registration with YARA pattern matching, A2A specification validation, and heuristic threat detection. Features include automatic tagging of unsafe agents, configurable blocking policies, and detailed scan reports with API endpoints for viewing results and triggering rescans.
- 🔧 Registry Management API - New programmatic API for managing servers, groups, and users. Python client (
api/registry_client.py) with type-safe interfaces, RESTful HTTP endpoints (/api/management/*), and comprehensive error handling. Replaces shell scripts with modern API approach while maintaining backward compatibility. API Documentation | Service Management Guide - ⭐ Server & Agent Rating System - Rate and review agents with an interactive 5-star rating widget. Users can submit ratings via the UI or CLI, view aggregate ratings with individual rating details, and update their existing ratings. Features include a rotating buffer (max 100 ratings per agent), one rating per user, float average calculations, and full OpenAPI documentation. Enables community-driven agent quality assessment and discovery.
- 🧠 Flexible Embeddings Support - Choose from three embedding provider options for semantic search: local sentence-transformers, OpenAI, or any LiteLLM-supported provider including Amazon Bedrock Titan, Cohere, and 100+ other models. Switch providers with simple configuration changes. Embeddings Guide
- ☁️ AWS ECS Production Deployment - Production-ready deployment on Amazon ECS Fargate with multi-AZ architecture, Application Load Balancer with HTTPS, auto-scaling, CloudWatch monitoring, and NAT Gateway high availability. Complete Terraform configuration for deploying the entire stack. ECS Deployment Guide
- Federated Registry - MCP Gateway registry now supports federation of servers and agents from other registries. Federation Guide
- 🔗 Agent-to-Agent (A2A) Protocol Support - Agents can now register, discover, and communicate with other agents through a secure, centralized registry. Enable autonomous agent ecosystems with Keycloak-based access control and fine-grained permissions. A2A Guide
- 🏢 Microsoft Entra ID Integration - Enterprise SSO with Microsoft Entra ID (Azure AD) authentication. Group-based access control, conditional access policies, and seamless integration with existing Microsoft 365 environments. Entra ID Setup Guide
- 🤖 Agentic CLI for MCP Registry - Talk to the Registry in natural language using a Claude Code-like interface. Discover tools, ask questions, and execute MCP commands conversationally. Learn more
- 🔒 MCP Server Security Scanning - Integrated vulnerability scanning with Cisco AI Defense MCP Scanner. Automatic security scans during server registration, periodic registry-wide scans with detailed markdown reports, and automatic disabling of servers with security issues.
- 📥 Import Servers from Anthropic MCP Registry - Import curated MCP servers from Anthropic's registry with a single command. Import Guide
- 🔌 Anthropic MCP Registry REST API Compatibility - Full compatibility with Anthropic's MCP Registry REST API specification. API Documentation
- 🔎 Unified Semantic Search for Servers, Tools & Agents - Natural-language search across every MCP server, its tools, and registered A2A agents using
POST /api/search/semantic. Works from the dashboard UI (session cookie auth) or programmatically with JWT Bearer tokens, returning relevance-scored matches per entity type in a single response. - 🚀 Pre-built Images - Deploy instantly with pre-built Docker images. Get Started | macOS Guide
- 🔐 Keycloak Integration - Enterprise authentication with AI agent audit trails and group-based authorization. Learn more
- 📊 Real-Time Metrics & Observability - Grafana dashboards with SQLite and OpenTelemetry integration. Observability Guide
- Amazon Bedrock AgentCore Integration - AgentCore Gateway support with dual authentication. Integration Guide
A2A Agents - Example Implementations
The registry includes two example A2A agents that demonstrate how both human developers and autonomous AI agents can discover, register, and use agents through the unified Agent Registry. Agents can programmatically discover other agents via semantic search and use them through the A2A protocol, enabling dynamic agent composition and autonomous agent orchestration.
Example Agents
| Agent | Path | Skills |
|---|---|---|
| Travel Assistant Agent | /travel-assistant-agent | Flight search, pricing checks, recommendations, trip planning |
| Flight Booking Agent | /flight-booking-agent | Availability checks, flight reservations, payments, reservation management |
Agent Discovery
View in Registry UI: Open the registry and navigate to the A2A Agents tab to browse registered agents with their full metadata, capabilities, and skills.
Search via Semantic API: Agents and developers can search for agents by natural language description:
# Search for agents that can help book a trip
cli/agent_mgmt.sh search "need an agent to book a trip"
Example Output:
Found 4 agent(s) matching 'need an agent to book a trip':
--------------------------------------------------------------------------------------------------------------
Agent Name | Path | Score
--------------------------------------------------------------------------------------------------------------
Travel Assistant Agent | /travel-assistant-agent | 0.8610
Flight Booking Agent | /flight-booking-agent | 1.2134
--------------------------------------------------------------------------------------------------------------
Agent Cards: View the agent card metadata at agents/a2a/test/ to see the complete agent definitions including skills, protocols, and capabilities.
For complete agent deployment and testing documentation, see agents/a2a/README.md.
Core Use Cases
AI Agent & Coding Assistant Governance
Provide both autonomous AI agents and human developers with secure access to approved tools through AI coding assistants (VS Code, Cursor, Claude Code) while maintaining IT oversight and compliance.
Enterprise Security & Compliance
Centralized authentication, fine-grained permissions, and comprehensive audit trails for SOX/GDPR compliance pathways across both human and AI agent access patterns.
Dynamic Tool Discovery
AI agents can autonomously discover and execute specialized tools beyond their initial capabilities using intelligent semantic search, while developers get guided tool discovery through their coding assistants.
Unified Access Gateway
Single gateway supporting both autonomous AI agents (machine-to-machine) and AI coding assistants (human-guided) with consistent authentication and tool access patterns.
Architecture
The MCP Gateway & Registry provides a unified platform for both autonomous AI agents and AI coding assistants to access enterprise-curated tools through a centralized gateway with comprehensive authentication and governance.
flowchart TB
subgraph Human_Users["Human Users"]
User1["Human User 1"]
User2["Human User 2"]
UserN["Human User N"]
end
subgraph AI_Agents["AI Agents"]
Agent1["AI Agent 1"]
Agent2["AI Agent 2"]
Agent3["AI Agent 3"]
AgentN["AI Agent N"]
end
subgraph EC2_Gateway["<b>MCP Gateway & Registry</b> (Amazon EC2 Instance)"]
subgraph NGINX["NGINX Reverse Proxy"]
RP["Reverse Proxy Router"]
end
subgraph AuthRegistry["Authentication & Registry Services"]
AuthServer["Auth Server<br/>(Dual Auth)"]
Registry["Registry<br/>Web UI"]
RegistryMCP["Registry<br/>MCP Server"]
end
subgraph LocalMCPServers["Local MCP Servers"]
MCP_Local1["MCP Server 1"]
MCP_Local2["MCP Server 2"]
end
end
%% Identity Provider
IdP[Identity Provider<br/>Keycloak/Cognito]
subgraph EKS_Cluster["Amazon EKS/EC2 Cluster"]
MCP_EKS1["MCP Server 3"]
MCP_EKS2["MCP Server 4"]
end
subgraph APIGW_Lambda["Amazon API Gateway + AWS Lambda"]
API_GW["Amazon API Gateway"]
Lambda1["AWS Lambda Function 1"]
Lambda2["AWS Lambda Function 2"]
end
subgraph External_Systems["External Data Sources & APIs"]
DB1[(Database 1)]
DB2[(Database 2)]
API1["External API 1"]
API2["External API 2"]
API3["External API 3"]
end
%% Connections from Human Users
User1 -->|Web Browser<br>Authentication| IdP
User2 -->|Web Browser<br>Authentication| IdP
UserN -->|Web Browser<br>Authentication| IdP
User1 -->|Web Browser<br>HTTPS| Registry
User2 -->|Web Browser<br>HTTPS| Registry
UserN -->|Web Browser<br>HTTPS| Registry
%% Connections from Agents to Gateway
Agent1 -->|MCP Protocol<br>SSE with Auth| RP
Agent2 -->|MCP Protocol<br>SSE with Auth| RP
Agent3 -->|MCP Protocol<br>Streamable HTTP with Auth| RP
AgentN -->|MCP Protocol<br>Streamable HTTP with Auth| RP
%% Auth flow connections
RP -->|Auth validation| AuthServer
AuthServer -.->|Validate credentials| IdP
Registry -.->|User authentication| IdP
RP -->|Tool discovery| RegistryMCP
RP -->|Web UI access| Registry
%% Connections from Gateway to MCP Servers
RP -->|SSE| MCP_Local1
RP -->|SSE| MCP_Local2
RP -->|SSE| MCP_EKS1
RP -->|SSE| MCP_EKS2
RP -->|Streamable HTTP| API_GW
%% Connections within API GW + Lambda
API_GW --> Lambda1
API_GW --> Lambda2
%% Connections to External Systems
MCP_Local1 -->|Tool Connection| DB1
MCP_Local2 -->|Tool Connection| DB2
MCP_EKS1 -->|Tool Connection| API1
MCP_EKS2 -->|Tool Connection| API2
Lambda1 -->|Tool Connection| API3
%% Style definitions
classDef user fill:#fff9c4,stroke:#f57f17,stroke-width:2px
classDef agent fill:#e1f5fe,stroke:#29b6f6,stroke-width:2px
classDef gateway fill:#e8f5e9,stroke:#66bb6a,stroke-width:2px
classDef nginx fill:#f3e5f5,stroke:#ab47bc,stroke-width:2px
classDef mcpServer fill:#fff3e0,stroke:#ffa726,stroke-width:2px
classDef eks fill:#ede7f6,stroke:#7e57c2,stroke-width:2px
classDef apiGw fill:#fce4ec,stroke:#ec407a,stroke-width:2px
classDef lambda fill:#ffebee,stroke:#ef5350,stroke-width:2px
classDef dataSource fill:#e3f2fd,stroke:#2196f3,stroke-width:2px
%% Apply styles
class User1,User2,UserN user
class Agent1,Agent2,Agent3,AgentN agent
class EC2_Gateway,NGINX gateway
class RP nginx
class AuthServer,Registry,RegistryMCP gateway
class IdP apiGw
class MCP_Local1,MCP_Local2 mcpServer
class EKS_Cluster,MCP_EKS1,MCP_EKS2 eks
class API_GW apiGw
class Lambda1,Lambda2 lambda
class DB1,DB2,API1,API2,API3 dataSource
Key Architectural Benefits:
- Unified Gateway: Single point of access for both AI agents and human developers through coding assistants
- Dual Authentication: Supports both human user authentication and machine-to-machine agent authentication
- Scalable Infrastructure: Nginx reverse proxy with horizontal scaling capabilities
- Multiple Transports: SSE and Streamable HTTP support for different client requirements
Key Advantages
Enterprise-Grade Security
- OAuth 2.0/3.0 compliance with IdP integration
- Fine-grained access control at tool and method level
- Zero-trust network architecture
- Complete audit trails and comprehensive analytics for compliance
AI Agent & Developer Experience
- Single configuration works across autonomous AI agents and AI coding assistants (VS Code, Cursor, Claude Code, Cline)
- Dynamic tool discovery with natural language queries for both agents and humans
- Instant onboarding for new team members and AI agent deployments
- Unified governance for both AI agents and human developers
Production Ready
- Container-native (Docker/Kubernetes)
- Real-time health monitoring and alerting
- Dual authentication supporting both human and machine authentication
Quick Start
There are 3 options for setting up the MCP Gateway & Registry:
- Option A: Pre-built Images — Fastest setup using pre-built Docker or Podman containers. Recommended for most users.
- Option B: Podman (Rootless) — Detailed Podman-specific instructions for macOS and rootless Linux environments.
- Option C: Build from Source — Full source build for customization or development.
Option A: Pre-built Images (Instant Setup)
Get running in under 2 minutes with pre-built containers:
Step 1: Clone and setup
git clone https://github.com/agentic-community/mcp-gateway-registry.git
cd mcp-gateway-registry
cp .env.example .env
Step 2: Download embeddings model Download the required sentence-transformers model to the shared models directory:
hf download sentence-transformers/all-MiniLM-L6-v2 --local-dir ${HOME}/mcp-gateway/models/all-MiniLM-L6-v2
Step 3: Configure environment Complete: Initial Environment Configuration - Configure domains, passwords, and authentication
export DOCKERHUB_ORG=mcpgateway
Step 4: Deploy with pre-built images Our service can be deployed with two platforms for pre-built images: Docker and Podman.
With Docker (default):
./build_and_run.sh --prebuilt
With Podman (rootless, macOS (but NOT Apple Silicon) friendly):
./build_and_run.sh --prebuilt --podman
# If running on macOS Apple Silicon, remove the --prebuilt flag (more details in Podman option below)
./build_and_run.sh --podman # For Apple Silicon
Port Differences:
- Docker: Services run on privileged ports (
http://localhost,https://localhost)- Podman: Services run on non-privileged ports (
http://localhost:8080,https://localhost:8443)- All internal service ports remain the same (Registry: 7860, Auth: 8888, etc.)
For detailed information about all Docker images used with --prebuilt, see Pre-built Images Documentation.
Step 5: Initialize Keycloak Complete: Initialize Keycloak Configuration - Set up identity provider and security policies
Step 5.5: Set up users and service accounts Run the bootstrap script to create default users and M2M service accounts:
./cli/bootstrap_user_and_m2m_setup.sh
This script:
- Creates 3 Keycloak groups:
registry-users-lob1,registry-users-lob2,registry-admins - Creates 6 users for testing and management:
- LOB1:
lob1-bot(M2M service account) andlob1-user(human user) - LOB2:
lob2-bot(M2M service account) andlob2-user(human user) - Admin:
admin-bot(M2M service account) andadmin-user(human user)
- LOB1:
- Generates and saves OAuth credentials to
.oauth-tokens/directory
All user passwords default to the value set in your .env file (INITIAL_USER_PASSWORD).
Step 6: Access the registry
open http://localhost:7860
Step 7: Create your first agent Complete: Create Your First AI Agent Account - Create agent credentials for testing
Step 8: Restart auth server to apply new credentials
docker-compose down auth-server && docker-compose rm -f auth-server && docker-compose up -d auth-server
Step 9: Test the setup Complete: Testing with mcp_client.py and agent.py - Validate your setup works correctly
Benefits: No build time • No Node.js required • No frontend compilation • Consistent tested images
Option B: Podman (Rootless Container Deployment)
Perfect for macOS and rootless Linux environments
Podman provides rootless container execution without requiring privileged ports, making it ideal for:
- macOS users with Podman Desktop
- Linux users preferring rootless containers
- Development environments where Docker daemon isn't available
Quick Podman Setup (macOS non-Apple Silicon):
# Install Podman Desktop
brew install podman-desktop
# OR download from: https://podman-desktop.io/
Inside Podman Desktop, go to Preferences > Podman Machine and create a new machine with at least 4 CPUs and 8GB RAM. Alternatively, see more detailed [Podman installation guide] (docs/installation.md#podman-installation) for instructions on setting this up on CLI.
# Initialize Podman machine
podman machine init
podman machine start
# Verify installation
podman --version
podman compose version
# Configure environment
cp .env.example .env
# Edit .env with your credentials
Deploy with Podman see full Podman setup instructions (downloading, installing, and initializing a first Podman container, as well as troubleshooting) in our Installation Guide.
Build with Podman:
# Auto-detect (will use Podman if Docker not available)
./build_and_run.sh --prebuilt
# Explicit Podman mode (only non-Apple Silicon)
./build_and_run.sh --prebuilt --podman
# Access registry at non-privileged ports
open http://localhost:8080
Note: Apple Silicon (M1/M2/M3)? Don't use
--prebuiltwith Podman on ARM64. This will cause a "proxy already running" error. See Podman on Apple Silicon Guide.
# To run on Apple Silicon Macs:
./build_and_run.sh --podman
Key Differences vs. Docker:
- No root/sudo required
- Works on macOS without privileged port access
- HTTP port:
8080(instead of80) - HTTPS port:
8443(instead of443) - All other service ports unchanged
For detailed Podman setup instructions, see Installation Guide and macOS Setup Guide.
Option C: Build from Source
New to MCP Gateway? Start with our Complete Setup Guide for detailed step-by-step instructions from scratch on AWS EC2.
Running on macOS? See our macOS Setup Guide for platform-specific instructions and optimizations.
Testing & Integration Options
Test Suite: The project includes comprehensive automated testing with pytest:
# Run all tests
make test
# Run only unit tests (fast)
make test-unit
# Run with coverage report
make test-coverage
# Run specific test categories
uv run pytest -m unit # Unit tests only
uv run pytest -m integration # Integration tests
uv run pytest -m "not slow" # Skip slow tests
Test Structure:
- Unit Tests (
tests/unit/) - Fast, isolated component tests - Integration Tests (
tests/integration/) - Component interaction tests - E2E Tests (
tests/integration/test_e2e_workflows.py) - Complete workflow tests
Python Agent:
agents/agent.py- Full-featured Python agent with advanced AI capabilities
Testing Documentation:
- Testing Guide - Comprehensive testing documentation
- Writing Tests - How to write effective tests
- Test Maintenance - Maintaining test suite health
Pre-commit Hooks:
# Install pre-commit hooks
pip install pre-commit
pre-commit install
# Run hooks manually
pre-commit run --all-files
Next Steps: Complete Installation Guide | Authentication Setup | AI Assistant Integration
Enterprise Features
AI Agents & Coding Assistants Integration
Transform how both autonomous AI agents and development teams access enterprise tools with centralized governance:
Enterprise-curated MCP servers accessible through unified gateway |
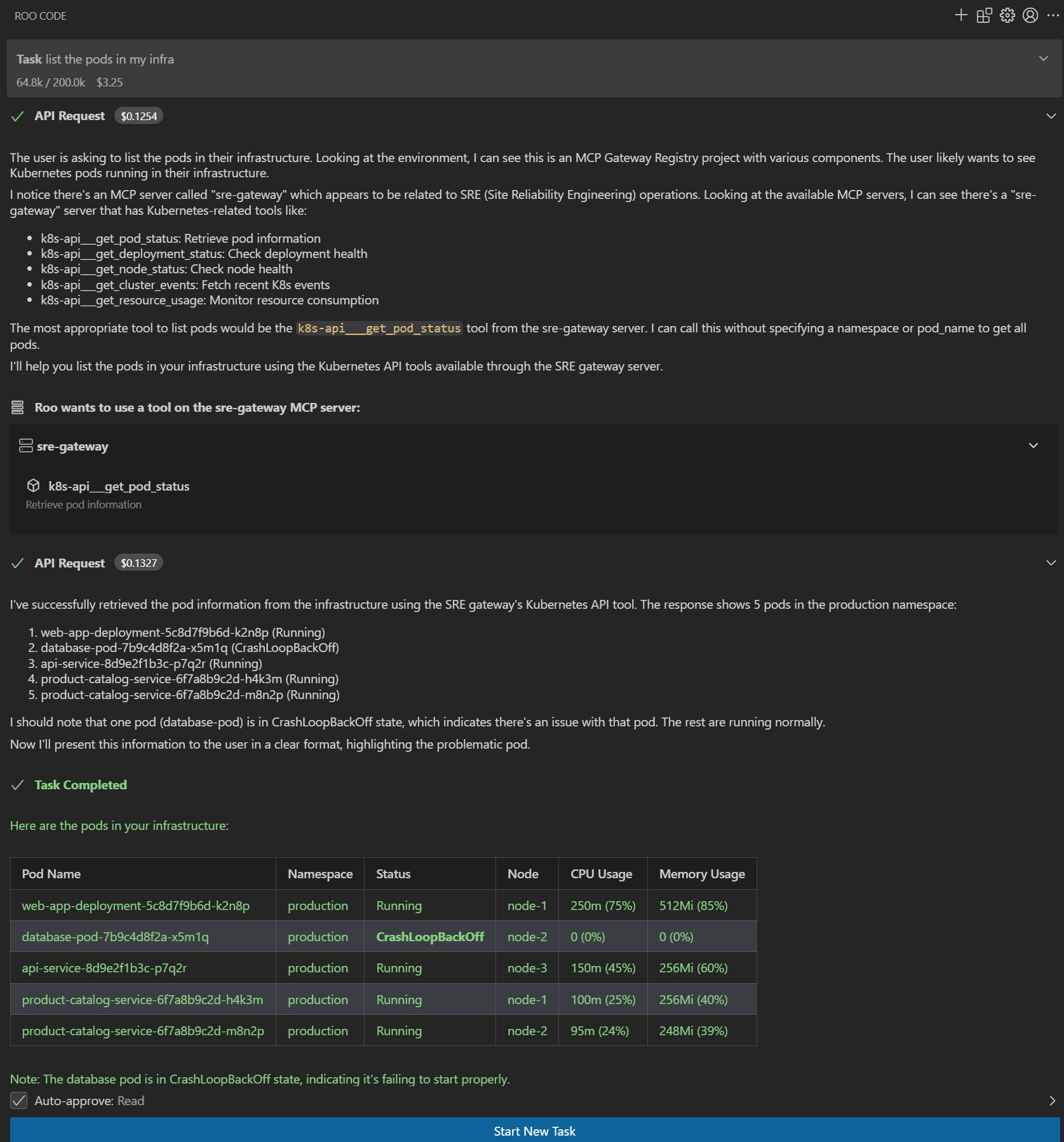
AI assistants executing approved enterprise tools with governance |
ObservabilityComprehensive real-time metrics and monitoring through Grafana dashboards with dual-path storage: SQLite for detailed historical analysis and OpenTelemetry (OTEL) export for integration with Prometheus, CloudWatch, Datadog, and other monitoring platforms. Track authentication events, tool executions, discovery queries, and system performance metrics. Learn more 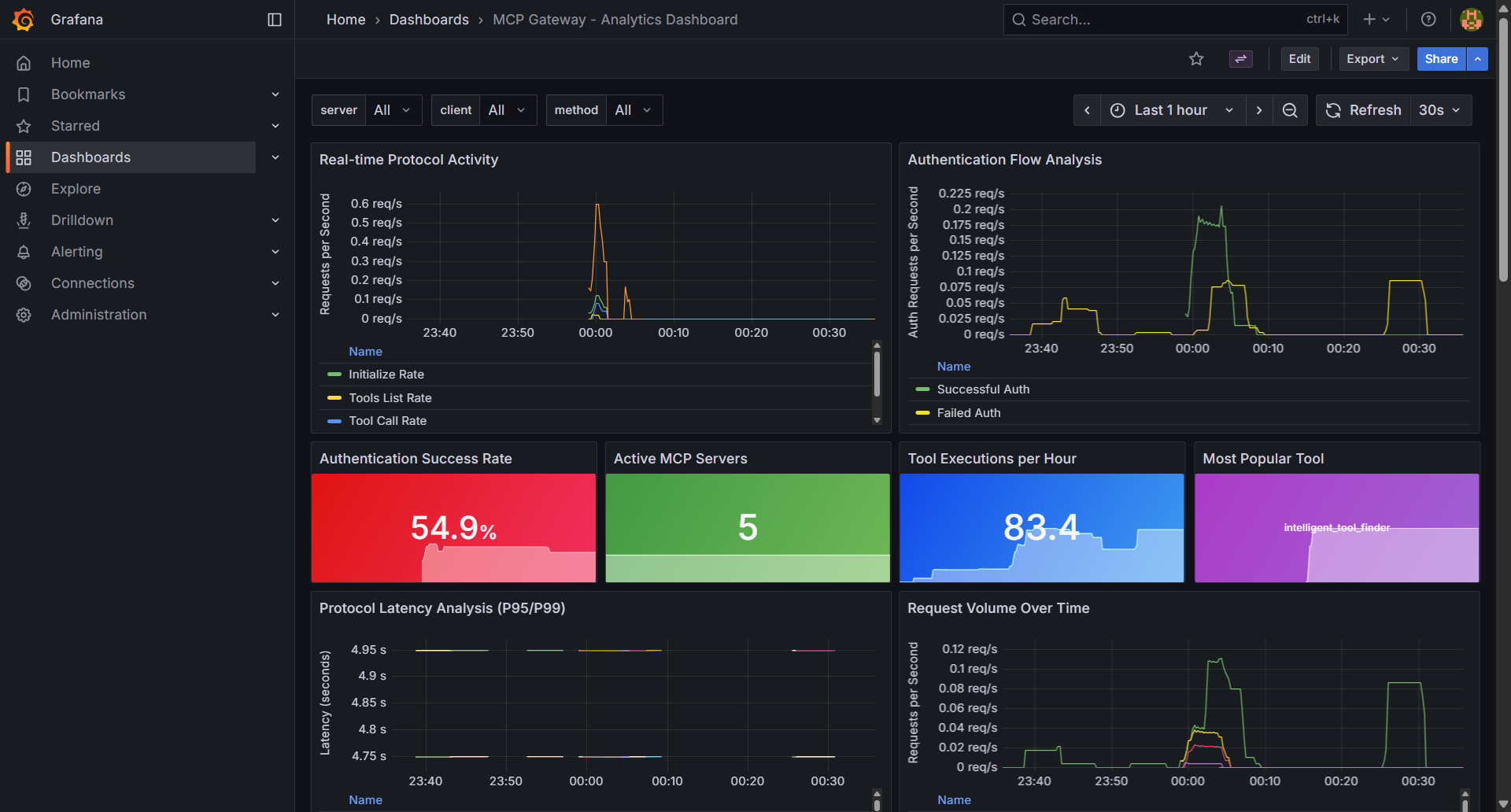
Real-time metrics and observability dashboard tracking server health, tool usage, and authentication events |
Anthropic MCP Registry Integration
Seamlessly integrate with Anthropic's official MCP Registry to import and access curated MCP servers through your gateway:
- Import Servers: Select and import desired servers from Anthropic's registry with a single command
- Unified Access: Access imported servers through your gateway with centralized authentication and governance
- API Compatibility: Full support for Anthropic's Registry REST API specification - point your Anthropic API clients to this registry to discover available servers
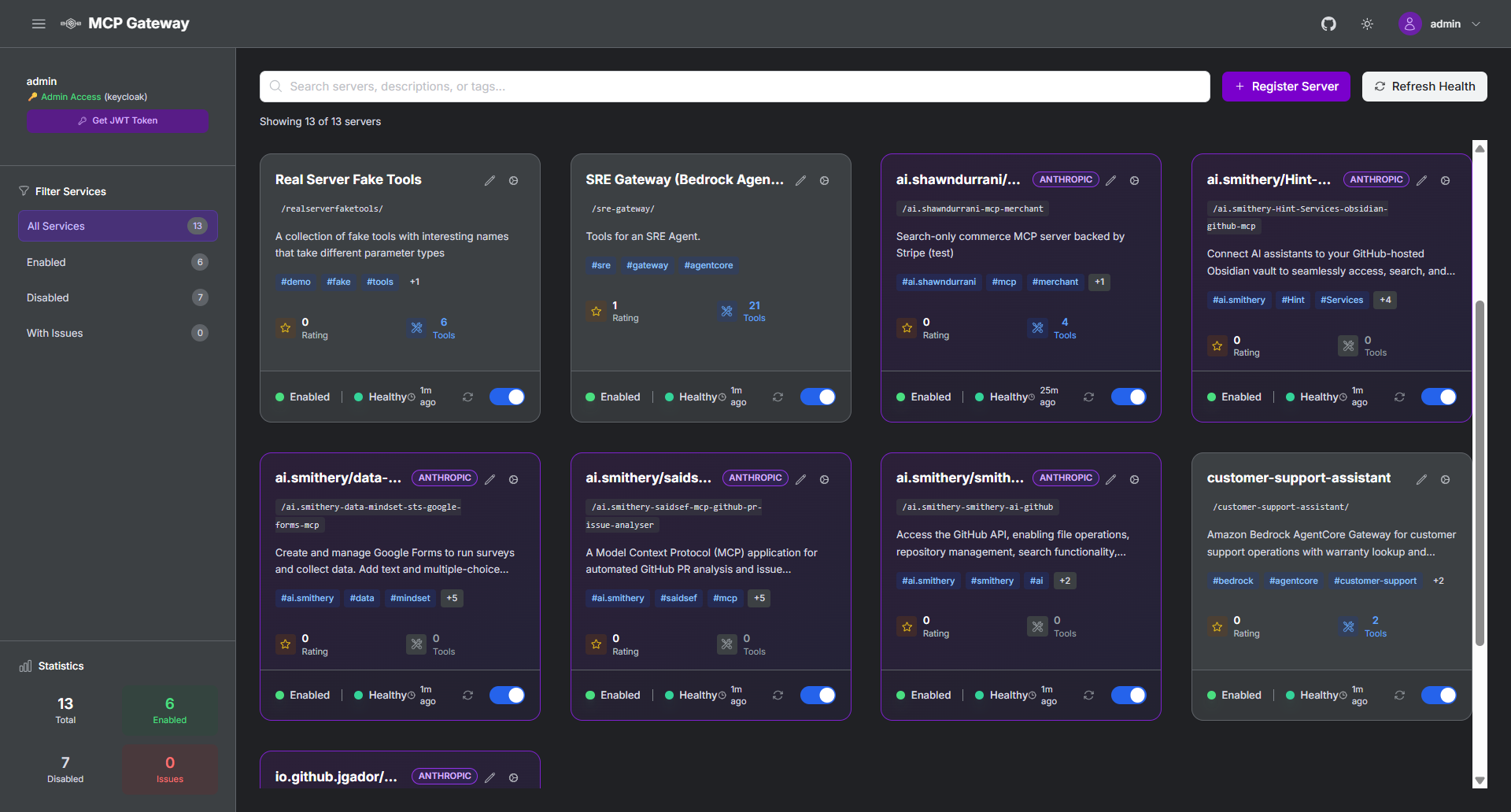
Import and access curated MCP servers from Anthropic's official registry
Import Guide | Registry API Documentation
Federation - External Registry Integration
Unified Multi-Registry Access:
- Anthropic MCP Registry - Import curated MCP servers with purple
ANTHROPICvisual tags - Workday ASOR - Import AI agents from Agent System of Record with orange
ASORvisual tags - Automatic Sync - Scheduled synchronization with external registries
- Visual Identification - Clear visual tags distinguish federation sources in the UI
- Centralized Management - Single control plane for all federated servers and agents
Quick Setup:
# Configure federation sources
echo 'ASOR_ACCESS_TOKEN=your_token' >> .env
# Update federation.json with your sources
# Restart services
./build_and_run.sh
📖 Complete Federation Guide - Environment setup, authentication, configuration, and troubleshooting
Security Scanning
Integrated Vulnerability Detection:
- Automated Security Scanning - Integrated vulnerability scanning for MCP servers using Cisco AI Defence MCP Scanner, with automatic scans during registration and support for periodic registry-wide scans
- Detailed Security Reports - Comprehensive markdown reports with vulnerability details, severity assessments, and remediation recommendations
- Automatic Protection - Servers with security issues are automatically disabled with security-pending status to protect your infrastructure
- Compliance Ready - Security audit trails and vulnerability tracking for enterprise compliance requirements
Authentication & Authorization
Multiple Identity Modes:
- Machine-to-Machine (M2M) - For autonomous AI agents and automated systems
- Three-Legged OAuth (3LO) - For external service integration (Atlassian, Google, GitHub)
- Session-Based - For human developers using AI coding assistants and web interface
Supported Identity Providers: Keycloak, Amazon Cognito, and any OAuth 2.0 compatible provider. Learn more
Fine-Grained Permissions: Tool-level, method-level, team-based, and temporary access controls. Learn more
Production Deployment
Cloud Platforms: Amazon EC2, Amazon EKS
Deployments
AWS Elastic Container Service (ECS)
Production-ready deployment on Amazon ECS Fargate with comprehensive enterprise features:
- Multi-AZ Architecture - High availability across multiple availability zones
- Application Load Balancer - HTTPS/SSL termination with automatic certificate management via ACM
- Auto-scaling - Dynamic scaling based on CPU and memory utilization
- CloudWatch Integration - Comprehensive monitoring, logging, and alerting
- NAT Gateway HA - High-availability NAT gateway configuration for secure outbound connectivity
- Keycloak Integration - Enterprise authentication with RDS Aurora PostgreSQL backend
- EFS Shared Storage - Persistent storage for models, logs, and configuration
- Service Discovery - AWS Cloud Map for service-to-service communication
Complete ECS Deployment Guide - Step-by-step instructions for deploying the entire stack with Terraform.
Amazon EKS (Kubernetes)
Coming Soon - Kubernetes deployment on Amazon EKS with Helm charts for container orchestration at scale.
Documentation
| Getting Started | Enterprise Setup | Developer & Operations |
|---|---|---|
| Complete Setup Guide NEW! Step-by-step from scratch on AWS EC2 | Authentication Guide OAuth and identity provider integration | AI Coding Assistants Setup VS Code, Cursor, Claude Code integration |
| Installation Guide Complete setup instructions for EC2 and EKS | AWS ECS Deployment Production-ready deployment on AWS ECS Fargate | API Reference Programmatic registry management |
| Keycloak Integration Enterprise identity with agent audit trails | Token Refresh Service Automated token refresh and lifecycle management | MCP Registry CLI Command-line client for registry management |
| Configuration Reference Environment variables and settings | Amazon Cognito Setup Step-by-step IdP configuration | Observability Guide NEW! Metrics, monitoring, and OpenTelemetry setup |
| Anthropic Registry Import NEW! Import servers from Anthropic MCP Registry | Federation Guide NEW! External registry integration (Anthropic, ASOR) | |
| Service Management Server lifecycle and operations | Anthropic Registry API NEW! REST API compatibility | |
| Fine-Grained Access Control Permission management and security | ||
| Dynamic Tool Discovery Autonomous agent capabilities | ||
| Production Deployment Complete setup for production environments | ||
| Troubleshooting Guide Common issues and solutions |
Community
Get Involved
Join the Discussion
- GitHub Discussions - Feature requests and general discussion
- GitHub Issues - Bug reports and feature requests
Contributing
- Contributing Guide - How to contribute code and documentation
- Code of Conduct - Community guidelines
- Security Policy - Responsible disclosure process
Star History
Roadmap
Our development roadmap is organized into weekly milestones with clear deliverables and progress tracking:
| Milestone | Due Date | Progress | Status | Key Issues |
|---|---|---|---|---|
| December 2025 Week 4 | 2025-12-27 | 43% (3/7) | 🚧 In Progress | Open: #317 - Optional PyTorch Dependencies, #293 - CloudFront HTTPS Support, #285 - Server Headers in Nginx, #232 - A2A Curated Registry Discovery Closed: #287 - Filter Sidebar Buttons, #284 - Statistics Count Fix, #221 - DocumentDB Implementation |
| January 2026 Week 1 | 2026-01-09 | 50% (2/4) | 🚧 In Progress | Open: #297 - Unified UI Registration Flow, #296 - Custom Metadata for Cards Closed: #329 - Update llms.txt, #259 - Simplify JWT Token Generation |
| January 2026 Week 3 | 2026-01-23 | 0% (0/2) | 📅 Planned | Open: #295 - Multi-Level Rate Limiting, #129 - Virtual MCP Server Support |
| January 2026 Week 4 | 2026-01-30 | 0% (0/2) | 📅 Planned | Open: #269 - AgentCore IAM Authentication, #260 - Federation Between Registries |
| Parking Lot | — | 50% (1/2) | 🗂️ Backlog | Open: #316 - Entra ID IAM APIs Closed: #315 - Distroless Docker Images |
Status Legend: 🚧 In Progress • 📅 Planned • 🗂️ Backlog • ✅ Complete
Major Features
The following major features span multiple milestones and represent significant architectural improvements:
-
#129 - Virtual MCP Server Support 🚧 IN PROGRESS (Jan 2026 Week 3) Dynamic tool aggregation and intelligent routing using Lua/JavaScript scripting. Enables logical grouping of tools from multiple backend servers.
-
#232 - A2A Curated Registry Discovery 🚧 IN PROGRESS (Dec 2025 Week 4) Enable agent-to-agent discovery and tool invocation through curated registry patterns.
-
#260 - Federation Between MCP Registry Instances 📅 PLANNED (Jan 2026 Week 4) Support for federated registry discovery and access across multiple registry instances.
-
#295 - Multi-Level Tool Usage Rate Limiting 📅 PLANNED (Jan 2026 Week 3) Comprehensive rate limiting architecture with detailed implementation guide for tool usage control.
-
#297 - Unified UI Registration Flow 🚧 IN PROGRESS (Jan 2026 Week 1) Streamlined registration experience for both MCP servers and A2A agents through a unified interface.
Recently Completed
-
#329 - Update llms.txt ✅ COMPLETED (v1.0.9) Updated AI assistant reference documentation with recent architecture changes.
-
#221 - DocumentDB Implementation ✅ COMPLETED (v1.0.9) Production-grade distributed storage with MongoDB/DocumentDB backend implementation.
-
#70 - Docker Build & Runtime Performance Optimization ✅ COMPLETED (v1.0.9) Multi-stage Docker builds with 66-80% image size reduction.
-
#287 - Filter Sidebar Buttons ✅ COMPLETED Fixed filter buttons to properly filter both MCP servers and A2A agent cards.
-
#284 - Statistics Count Fix ✅ COMPLETED Sidebar statistics now correctly count both MCP servers and A2A agents.
-
#259 - Simplify JWT Token Generation ✅ COMPLETED Streamlined JWT token generation process in Registry UI.
-
#315 - Distroless Docker Images ✅ COMPLETED Security hardening through migration to distroless/hardened base images.
For the complete list of all issues, feature requests, and detailed release history, visit:
License
This project is licensed under the Apache-2.0 License - see the LICENSE file for details.
⭐ Star this repository if it helps your organization!




