..:: SysPlant ::..
Your Syscall Factory (feat. Canterlot's Gate)

SysPlant is a python generation tool of the currently known syscall hooking methods. It currently supports following gates (aka: iterators):
- Hell's Gate : Lookup syscall by first opcodes
- Halos's Gate : Lookup syscall by first opcodes and search nearby if first instruction is a JMP
- Tartarus' Gate : Lookup syscall by first opcodes and search nearby if first or third instruction is a JMP
- FreshyCalls : Lookup syscall by name (start with Nt and not Ntdll), sort addresses to retrieve syscall number
- SysWhispers2 : Lookup syscall by name (start with Zw), sort addresses to retrieve syscall number
- SysWhispers3 : SysWhispers2 style but introduce direct/indirect/random jump with static offset
- Canterlot's Gate ! :unicorn: :rainbow: (from an initial idea of MDSEC article) but who was missing a pony name : Lookup syscall using Runtime Exception Table (sorted by syscall number) and detect offset to syscall instruction for random jumps.
- Custom Allows you to choose an iterator and a syscall stub method (direct / indirect / random / egg_hunter) which describe the way your NtFunctions will be effectively called.
:warning: DISCLAIMER
Please only use this tool on systems you have permission to access.
Usage is restricted to Pentesting or Education only.
All credits are based on my own research, please feel free to claim any method if I made mistakes...
Introduction
This personal project aims to be a simple tool to better understand & generate different syscall retrieval methods, and being able to play with direct / indirect / egg_hunter syscall stub. The first goal was to get my hands into NIM and then it overflow to C and Rust :wink: ...
SysPlant has been developped for Linux users, some stuff might be broken within Windows or Mac. PR are welcome if you found anything that does not work as expected.
Supported Languages
| Language | Status | Cross-compile from Linux |
|---|---|---|
| NIM | :white_check_mark: Stable | nim c -d=release -d=danger -d=strip --opt=size -d=mingw --cpu=amd64 |
| C | :white_check_mark: Stable | x86_64-w64-mingw32-gcc -Wall -s -static -masm=intel |
| Rust | :white_check_mark: Stable | cargo build --release --target x86_64-pc-windows-gnu |
MCP Server
SysPlant ships with a built-in Model Context Protocol (MCP) server, allowing AI coding assistants (Claude Code, Cursor, Windsurf, etc.) to generate syscall code directly from their chat interface.
# stdio (default — plug into your AI client)
python bridge_mcp_sysplant.py
# SSE or Streamable HTTP for web-based clients
python bridge_mcp_sysplant.py --transport sse --port 9090
See the full guide: Sysplant as a MCP server
General usage
$ sysplant -h
usage: main.py [-h] [--debug | --verbose | --quiet] {list,generate} ...
..:: SysPlant - Your Syscall Factory ::..
positional arguments:
{list,generate}
options:
-h, --help show this help message and exit
Output options:
--debug Display all DEBUG messages upon execution
--verbose Display all INFO messages upon execution
--quiet Remove all messages upon execution
$ sysplant generate -h
usage: main.py generate [-h] [-x86 | -wow | -x64] [-nim | -c | -rust]
[-p {all,donut,common} | -f FUNCTIONS] [-x] -o OUTPUT
{hell,halo,tartarus,freshy,syswhispers,syswhispers3,canterlot,custom}
...
options:
-h, --help show this help message and exit
-x, --scramble Randomize internal function names to evade static analysis
-o OUTPUT, --output OUTPUT
Output path for generated file
Architecture options:
-x86 Set mode to 32bits
-wow Set mode to WoW64 (execution of 32bits on 64bits)
-x64 Set mode to 64bits (Default True)
Language options:
-nim Generate NIM code (Default: true)
-c Generate C code
-rust Generate Rust code
Syscall options:
-p {all,donut,common}, --preset {all,donut,common}
Preset functions to generate (Default: common)
-f FUNCTIONS, --functions FUNCTIONS
Comma-separated functions
Example output
Here is an example of C syscall generation using Canterlot's Gate iterator:
$ sysplant generate -c -o syscalls.c canterlot
⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⢠⠶⢤⡀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀
⠀⢀⣀⡀⠀⢀⣠⣤⣴⣶⣶⡦⠤⢤⣤⣀⣀⣼⠀⠀⡽⣄⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀
⠀⠈⠫⣯⠙⡟⢿⣿⣿⡿⠁⠀⢠⣾⣿⣿⣿⡿⠀⠀⢹⠘⡆⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀
⠀⠀⣼⣿⣷⣧⡀⢱⠈⠀⠀⠀⣿⣿⣿⣿⣿⡀⠀⠀⢸⠀⢳⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀ ⠀⠀..:: SysPlant - Your Syscall Factory ::..
⠀⣼⣿⣿⣿⣿⣿⣿⡄⢀⣀⣠⣿⣿⣿⠿⢿⣷⣤⡀⠈⠀⡟⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀
⢠⣿⣿⣿⣿⣿⣿⠿⠛⠉⠉⠀⡇⣾⣿⣦⣀⣿⡄⠀⠀⢰⠃⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀ ⠀⠀⠀⠀⠀⠀⠀⠀⠀ Sysplant (2023) - 0x42en
⢸⣿⣿⣿⠿⢯⣷⢄⠀⠀⠀⠀⡄⢻⣿⣯⣻⣿⡧⠄⠀⢸⠀
⠘⣿⠟⠁⠀⠚⢻⣦⣱⣄⠀⠀⢣⠈⠛⣽⣿⠿⠭⠀⣠⣿⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⢀⣠⡤⠶⠶⠶⠶⢤⣄⡀⠀⠀⠀⠀⠀ Canterlot's Gate (2022) - @MDSecLabs
⠀⠁⠀⠀⠀⠀⠀⠻⣿⣿⠀⠀⠈⠂⠀⠀⢀⣄⣠⣴⣿⣿⠀⠀⠀⠀⠀⠀⠀⠀⠀⣠⠶⠋⠁⠀⠀⠀⠀⠀⠀⠀⠉⠳⢦⡀⠀ @0x42en
⠀⠀⠀⠀⠀⠀⠀⠀⣸⠋⠄⢠⠀⠀⠀⠀⣾⣿⣿⣿⣿⣿⡀⠀⠀⠀⠀⠀⠀⠀⡴⠃⠀⣠⣤⣶⣶⣾⣶⣶⣦⣄⠀⠀⠀⠹⣆⠀⠀⠀⠀ Syswhispers3 (2022) - @klezVirus
⠀⠀⠀⠀⠀⠀⠀⠀⠈⠲⠴⠯⠤⠤⢶⢾⣿⣿⣿⣿⣿⠏⠷⣄⢀⣀⣀⣀⡀⣼⣠⣴⣿⣿⣿⣿⣿⣿⣿⣿⣿⣿⣷⡀⠀⠀⠸⣧⠀⠀ Syswhispers2 (2021) - @Jackson_T
⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⢠⠏⠈⠉⣡⣾⣿⠏⠀⢰⣿⠉⣩⠀⠉⢙⣿⡿⠛⠉⠉⠙⠛⢿⣿⣿⣿⣿⣿⣿⣷⠀⠀⠀⢻⣇⠀ @modexpblog
⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⢀⡟⠀⠀⣿⣿⡿⠋⠀⢀⣾⡿⠀⣉⣀⣇⠘⠋⣿⠀⠀⠀⠀⠀⠀⠙⣿⣿⣿⣿⣿⣿⡆⠀⠀⢸⣿⡆ Tartarus' Gate (2021) - @trickster0
⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⢸⠃⠀⠀⠘⢯⡀⠀⢀⣾⣿⠇⣴⠨⣿⣿⡯⠀⢸⠀⠀⠀⠀⠀⠀⠀⠘⣿⣿⣿⣿⣿⡇⠀⠀⢸⣿⣷ Halo's Gate (2021) - @Sektor7net
⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠸⡆⠀⠀⠀⠈⠻⢦⣾⣿⠏⠀⠈⢈⣝⡟⠁⣶⣾⠀⠀⠀⠀⠀⠀⠀⠀⢹⣿⣿⣿⣿⡇⠀⠀⢸⣿⣿⡀ FreshyCalls (2020) - @crummie5
⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⢻⡀⢄⣀⡀⠀⠀⠉⠁⠀⠰⣄⠀⠁⠀⠀⢀⡏⠀⠀⠀⠀⠀⠀⠀⠀⠈⣿⣿⣿⣿⠃⠀⠀⣸⣿⣿⡇ Hell's Gate (2020) - @RtlMateusz
⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠈⢷⡀⢹⠁⠀⢠⠶⠤⠤⢴⡾⢦⡀⠀⠀⣼⠦⡄⠀⠀⠀⠀⠀⠀⠀⠀⣿⣿⣿⣿⠀⠀⠀⣿⣿⣿⠇ @am0nsec
⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠈⣷⠇⠀⠀⢸⡄⠀⠀⠀⠙⢆⠙⢦⡀⠀⠀⠙⣦⠀⠀⠀⠀⠀⠀⠀⣿⣿⣿⡇⠀⠀⢰⣿⡿⠋⠀
⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⢀⡟⠀⠀⠀⡟⢻⡀⠀⠀⠀⠈⢳⡀⢳⡀⠀⠀⠈⢧⡀⠀⠀⠀⠀⠀⣿⣿⣿⠁⠀⢀⣼⠟⠁⠀⠀
⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⢀⡞⠀⠀⠀⠀⡇⠀⢧⠀⠀⠀⠀⠀⢷⠀⢳⠀⠀⠀⠈⢧⠀⠀⠀⠀⢀⣿⣿⡏⢀⣴⠟⠁⠀⠀⠀⠀
⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⢀⡞⠀⠀⠀⠀⢸⠇⠀⠸⡆⠀⠀⠀⠀⢸⠀⢸⡇⠀⠀⠀⠘⣧⠀⠀⠀⢸⣿⣿⡷⠛⠁⠀⠀⠀⠀⠀⠀
⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⢀⡞⠀⠀⠀⠀⠀⣾⠀⠀⠀⣧⠀⠀⠀⠀⢸⠀⠀⡇⠀⠀⠀⠀⢸⡆⠀⠀⣿⠿⠋⠀⠀⠀⠀⠀⠀⠀⠀⠀
⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⢠⠎⠀⠀⠀⠀⠀⣰⠇⠀⠀⠀⣿⠀⠀⠀⠀⣏⣀⣸⠇⠀⠀⠀⠀⠀⣷⠀⠈⠁⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀
⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠻⠤⣤⣤⣤⡤⠴⠛⠛⠛⠛⠉⠁⠀⠀⠀⠀⠈⠉⢿⣄⣀⣠⣤⡤⠶⠋⠀⠀⠀⠀⠀⠀⠀⠀
[+] Summary of params used
. Language: C
. Architecture: x64
. Selected syscall iterator: canterlot
. Selected syscall caller stub: random
. Common supported functions selected
. Randomize internal function: False
[+] Syscall file written to syscalls.c.h
What is iterator option ?
Sysplant is based on existing mechanisms for syscall number and addresses retrieval. I do not claim any of their discovery, I just harmonize all this methods in a single tool to be able to generate them easily using templates. These mechanisms are called iterator, if you look at the code you'll probably understand why :wink:
If you want to go further in the explanations of what is a syscall ? you should check @Alice Climent blogpost about syscalls techniques
What is method option ?
Once your iterator has been choosen you can then specify a method option based on the existing way to call syscalls. All the iterator are supported which let you select whatever you want as a final syscall stub.
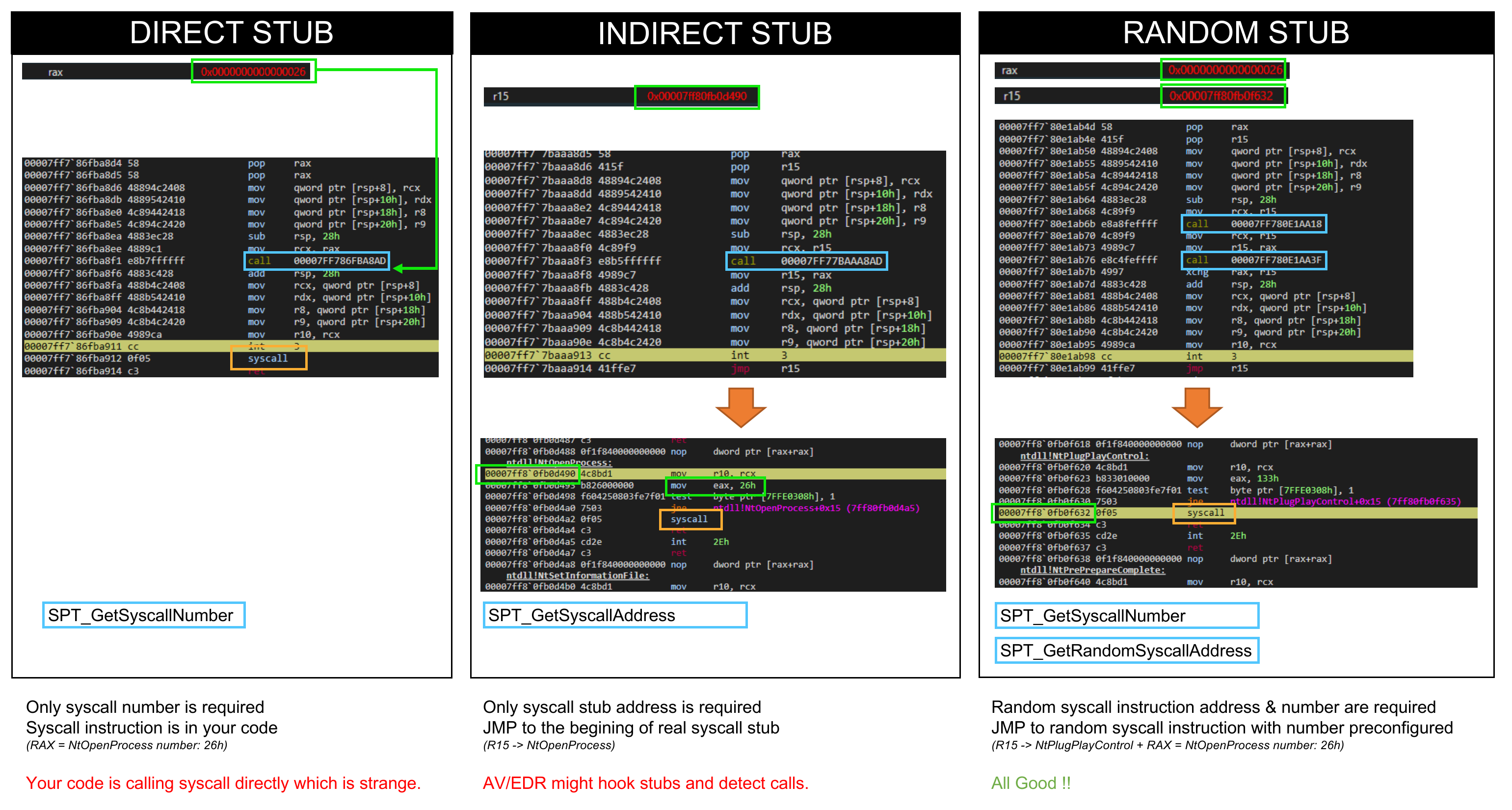
- Direct: the syscall is made directly in the Sysplant ASM call. You only need the syscall number but AV/EDR might see you...
- Indirect: the Sysplant ASM call jump to the begining of Ntdll stub. You only need syscall address and no longer call syscall in your code but AV/EDR might hook these functions
- Random: the Sysplant ASM call jump to a random syscall instruction of Ntdll stubs. You need the syscall number and 1 syscall instruction address. You then no longer call syscall in your code and can avoid hooked functions.
- Egg Hunter: the inline
syscallinstruction is replaced by a random 8-byte marker (the egg). At runtime, callSPT_SanitizeSyscalls()before any Nt* function to scan the.textsection and patch every egg back tosyscall; ret. This avoids static signatures on the0F 05opcode while keeping direct-call performance.
Documentation
I've tried to keep an up to date documentation, so please READ THE DOC. You will find there many information about the tool's usages and a complete description of the classes and methods.
Some specifics usages are described:
Credits
Massive shout-out to these useful projects that helps me during this journey, or individuals for their reviews
- @alice blogpost about syscalls techniques
- @redops blogpost about direct vs indirect syscalls
- @Jackson_T & @modexpblog for Syswhispers2
- @klezvirus for syswhispers3
:construction: TODO
This project is in WIP state...
Some PR & reviews are more than welcome :tada: !
- Add internal names randomization
- Setup documentation
- Setup tests
- Add x86 support
- Add WoW64 support
- Setup NIM templates
- Setup C templates
- Setup Rust templates
- Setup Go / CPP / C# / Whatever templates
License
This project is licensed under the GPLv3 License, for individuals only. If you want to integrate this work in your commercial project please contact me through 0x42en[at]gmail.com